How to protect your mobile devices and online privacy

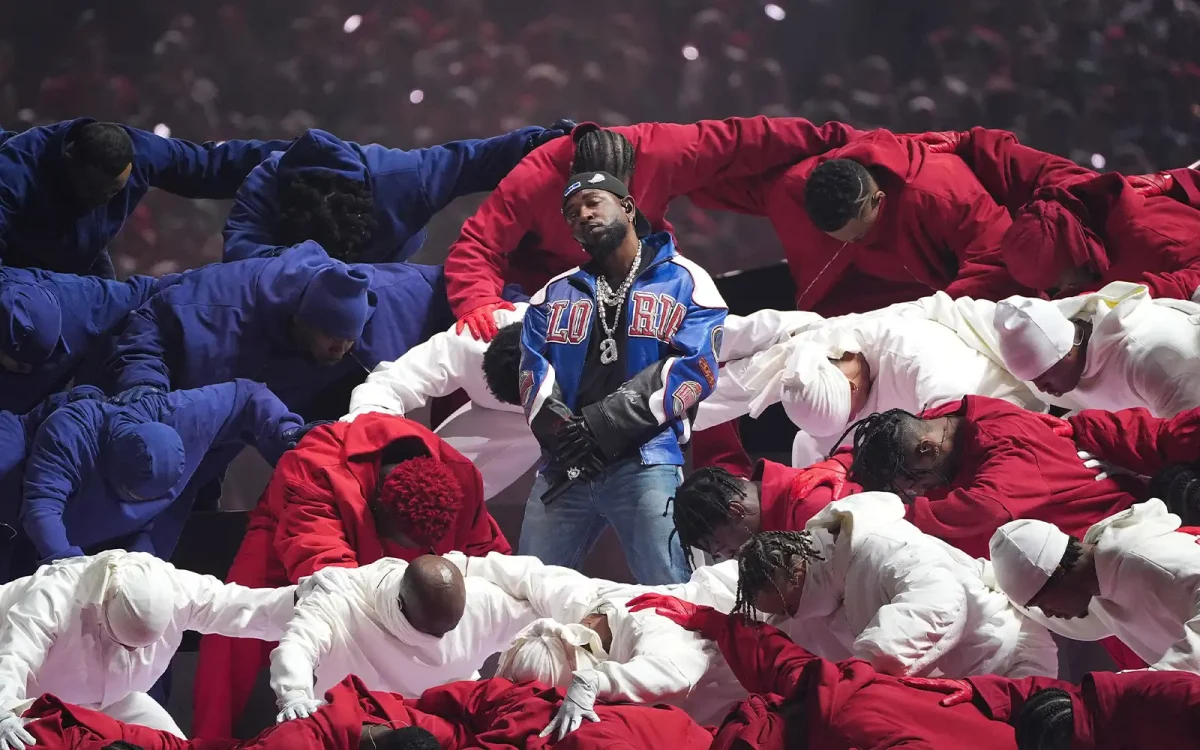
Wikileaks released a series of documents in a release named “Vault 7” that describes the vast cyber capabilities of the CIA. Photo by Kyle Hammalian.
Wikileaks, an online nonprofit that publishes secret and classified materials, leaked thousands of documents associated with the Central Intelligence Agency’s (CIA) hacking program and its far-reaching capabilities on March 7. The release, named Vault 7, detailed the agency’s ability to hack Androids, iPhones, Smart TVs, and Microsoft, Mac, and Linux operating systems. It also described explorations into hacking cars, which Wikileaks says could be used for nearly “undetectable assassinations.”
Other capabilities include the agency’s ability to hack encrypted chat platforms to view private messages, even on secure messaging apps like WhatsApp. A leaked document titled “Fine Dining” describes instances that the CIA used their ability to hack different computer operating systems to spy on targets through malware-laced versions of popular apps, such as Skype, 2048, Prezi, or NotePad++.
The CIA program “Weeping Angel” describes capabilities to hack into devices like the Smart TV, or other smart products, to listen to conversations happening around the device, even when it appears to be turned off.
There’s no evidence to suggest that the CIA is spying on citizens, which would be illegal since the CIA cannot operate within the United States, however the leaks are a reminder of the vulnerability of many of our devices. The CIA hid many of the vulnerabilities they exploited, leaving them open to hackers and foreign governments to abuse.
Aside from simply unplugging, here are some tips to protect your devices and general online privacy in the future:
Update your devices and software
The CIA has been working hard to crack Apple’s encryptions, and Apple has publicly announced they have patched most vulnerabilities in their iOS system. The Wikileaks documents discussed vulnerabilities in iOS up to the 8.2 operating system. It’s important to always update your operating system on mobile devices and personal computers with the most recent suggested software, as these tend to include important security updates and vulnerability patches. This includes web browsers–it’s much more important to have an updated browser than the browser you use.
Use strong and unique passwords
Websites like How Secure Is My Password allow you to test the strength of your password by showing you how many milliseconds to years it would take to crack a password, along with other suggestions for strengthening it. Don’t use the same password for everything either, and consider using a password manager. This video from Vox explains why you should use a password manager, an app that encrypts passwords in a “digital safe” and is secured with a strong master password.
Two-factor authentication
Two-factor authentication is a very strong way to prevent people from accessing your accounts, but only certain websites offer it. Google users can use it for their accounts, and Apple users can use it for their Apple ID. Basically, anytime you log in on a new device, it sends a text or email to you with a six digit code. It may seem like a hassle, but it only has to be done once on every new device, and is a good way to monitor account activity.
Use antivirus software
Antivirus software is a must-have to maintain your personal security, and it’s available on all platforms. For macs, Sophos Home is a free antivirus program that even our school computers use. Antivirus software detects viruses, malware, and ransomware from computers and prevents them from executing.
Use secure websites (HTTPS)
Notice that some websites begin with HTTPS, while others begin with HTTP. Websites that begin with HTTPS, which stands for Hypertext Transfer Protocol Secure, are safer to use and prevent third parties from any malicious activities that may put your privacy at risk. While a website with only HTTP isn’t necessarily unsafe, it could be, so you definitely should not enter sensitive information, like credit card numbers, here. Browsers like Google Chrome identify websites with their ‘Secure’ logo.
Avoid phishing
Phishing is a type of scam where a website or an email looks like it is from a real company, but it’s actually a fraudulent attempt to obtain your personal information. These typically end up in spam mailboxes, but just as good practice: Never click a link to a site like a bank account or Paypal that appears in your email.
Consider the information you’re putting online
Consider the information you’re putting on public profiles and providing to websites, especially when it’s voluntary. Be careful what you post on websites like Facebook. Even information that seems harmless, like the fact that you’re on vacation, can be used against you or someone you know. For example, scammers sometimes call elderly family members and make fraudulent demands for money, often pretending to have been arrested or kidnapped on vacation. In some cases, burglars may find houses to rob when they know a family is away.